“She Stole My Life!”: A Cautionary True Tale About Identity Theft Everyone Must Read
Updated: Jun. 16, 2021
“She Stole My Life!”: A Cautionary True Tale About Identity Theft Everyone Must Read
 Retired nurse Helen Anderson* was an irresistible mark. To an identity thief like Alice Lipski, this was a woman from another time and place, with little Internet access and paper bank statements that were sent to her unlocked mailbox. Becoming Anderson was a cinch. So Lipski went to Macy’s and treated herself to a shopping spree, courtesy of the retiree. She roved the Seattle store, charging clothes at three registers.
Retired nurse Helen Anderson* was an irresistible mark. To an identity thief like Alice Lipski, this was a woman from another time and place, with little Internet access and paper bank statements that were sent to her unlocked mailbox. Becoming Anderson was a cinch. So Lipski went to Macy’s and treated herself to a shopping spree, courtesy of the retiree. She roved the Seattle store, charging clothes at three registers.
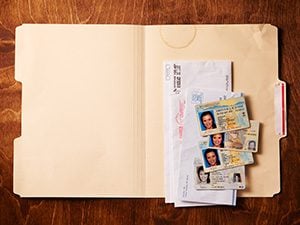
But when Lipski exited, she made a mistake. She left behind, on a chair where it sat like a time bomb, her purse. Inside were the tools of her trade: a computer and ten driver’s licenses in nine names but each with Lipski’s face.
There is an Alice Lipski in almost every city and town. Some 16.6 million people in the United States were victims of identity theft in 2012, according to the Department of Justice, with losses totaling $24.7 billion, and the number of victims appears to be rising. Older people are particularly attractive targets. Compared with the young, they tend to have better credit and more accounts. Technology has made it easier for criminals to utilize the elderly’s personal and financial data. Older adults are also less likely to have online access to their bank and credit card accounts, so they’re not monitoring their activity so closely.
Most methods of identity theft fall into one of two categories: low tech and high tech, according to Melinda Young, a King County prosecuting attorney who supervised the case against Lipski. “High-tech thieves are more tied to organized crime and do the sophisticated breaches,” Young says. Those are the headline-making crimes like the Target hack in November 2013, when thieves stole some 40 million credit card numbers. Al Pascual, a senior research analyst for Javelin Strategy & Research, says hackers have gotten better at capitalizing on these security breaches. In 2010, one in nine consumers who received breach notifications became a fraud victim, and “by 2014,” Pascual says, “it was one in eight.” Meanwhile, low-tech thieves “steal mail and burglarize cars and houses to get information,” Young explains.
But what if the thief is both: a street criminal who also has the digital smarts of a hacker? In the fall of 2012, 64-year-old Helen Anderson was about to find out.
Retirement for her came suddenly. For most of her adult life, she worked in the OR at a Seattle hospital. Like many nurses, she developed back problems. One day in 2011, her legs hurt; by evening, she couldn’t walk. She had back surgery, which restored her mobility, but she was unable to return to work.
Luckily, Anderson had planned well. She had good credit, paid her bills on time, and owned her home. When she retired, her daughter, who lived in Portland, Oregon, was having health problems. Anderson went to Portland in August to help, letting her niece, Samantha, house-sit. Anderson’s only condition: Don’t let anyone stay with you.
When Anderson returned in October, she was surprised to discover a woman named Alice Lipski there. Alice, her niece explained, was a friend. She’d had a fight with her boyfriend and needed a place to live. Samantha had let her stay for a few days. Anderson told Samantha that Lipski had to be out by the end of the week.
Mailboxing is like hunting for gold but far easier—and Lipski and her crew were pros at it. Most people don’t lock their mailboxes, so crooks just pull out the treasure: bank statements, credit card offers, and credit union applications. January, when people receive W-2 tax forms, is prime hunting season. The team also broke into cars, like the ones sitting in the long-term lot at the train station or the vehicles in a gym parking lot, because people frequently left their wallets in them during workouts.
The average car is full of useful stuff. Those gas station and ATM receipts? They may have partial account numbers and bank names. Of course, if a driver kept a vehicle registration in the car, the thieves could instantly learn their mark’s name and address—two pieces of the puzzle. Then they’d hit the person’s home mailbox until they had everything they needed.
Next they’d counterfeit IDs. Dino, a member of Lipski’s crew, was the artist who made them. Their friend Brian was security; he rigged an encrypted server to store their stolen data. Lipski was the face of the operation, a pretty, well-spoken woman who could stride into a bank without raising eyebrows. She could present a bogus driver’s license and walk out with hundreds of dollars. But there was a fourth member of the crew.
Lipski was first given methamphetamines in 1996 at 17. Her parents split soon after she was born; her dad raised her. Lipski saw her birth mother in the summer. On one visit, her mother’s friend passed her a meth pipe. She inhaled, and like her mom, she became an addict.
Law enforcement officials have long known about the link between meth addicts and ID theft. Some experts say that half or more of the identity thieves who get prosecuted are addicts. Tweakers—slang for users—can stay awake for days at a time, thinking up ways to get more money for drugs.
At first, Lipski wasn’t involved in fraud. But everyone in her crowd of users was doing it. She’d watch and offer ideas. “Once I found out I was good at this, it was on,” she says. Then she met Dino, the fake-ID genius: “He and I would sit around getting high and brainstorming. Together, we were a complete fraud nightmare.”
Lipski had established a network of runners when she used to deal meth. After getting into identity theft, she’d send them to steal mail and break into cars. Lipski would take information from the runners and hit the Web to find birthdays, family names, and past addresses. Armed with a dossier of likely passwords and personal data, she’d set up new accounts and profiles.
She loved beating the system. “These are billion-dollar companies with huge security features,” she says, “and I was able to get through them. It’s a huge ego boost.” And, she reasoned, she wasn’t hurting anyone. The strangers whose names and accounts she stole were covered; the banks and credit card companies were the ones on the hook for losses.
When Samantha let Lipski stay at her aunt’s home in 2012, Lipski was primed to take advantage of the situation. The house was full of receipts and mail—an ID thief’s paradise.
The manager of Anderson’s credit union called her on Thursday, October 25, shortly after she’d returned from Portland. Her account was overdrawn—someone had charged $300 on a new debit card, one that Anderson had never used.
On Monday, Anderson went to the credit union office to fill out a fraud affidavit. The money was restored, and the problem was settled. A few days later, a call came from Wells Fargo. Had she just made $5,000 in charges on a credit card? The card was recently activated, and an initial balance had been paid with a credit union check to boost the spending limit.
Anderson returned to the credit union. While looking at her account, the manager asked, “Did you pay $500 from this checking account toward your American Express bill online?” No—she never paid bills online.
A few miles away, Alice Lipski was taking over Anderson’s identity. She signed Anderson up for a credit-monitoring service that was designed to protect customers from identity theft. Instead, it exposed her full credit history. The report revealed a mother lode of old accounts; over her life, Anderson had acquired dozens of cards from stores and banks. Most were inactive. Lipski reported those as lost or stolen, so the companies assigned new numbers with new usernames, passwords, and security questions that only Lipski knew, locking Anderson out of the accounts. “I knew everything about her,” Lipski says. “And what I didn’t know, I changed to what I wanted it to be.” She ordered Anderson’s mail forwarded to Lipski’s boyfriend’s house, then to a post office box. Since Anderson still received junk mail, it took weeks for her to notice that checks and bills had stopped coming.
Anderson got more calls from credit card companies about suspicious transactions—casino bills, charges for new tires, fancy wheel covers, gas, food, clothes. In six months, more than $30,000 was spent in her name.
Anderson felt like a foreigner moored in a country whose language and customs she couldn’t decipher: “I would call a card company. They’d ask for the account number and password, and I couldn’t give them either one.” All she could do was go to the banks and stores in person and show their employees her driver’s license to prove who she was. She’d cancel the cards. Then, a fresh wave of attacks.
Here’s one thing you learn only after identity theft happens to you: You vanish. So thorough was Lipski’s intrusion that Anderson found herself arguing with bank officers over personal details like her old jobs, addresses, and mother’s maiden name. “I couldn’t prove who I was, because she could prove it easier than I could,” she says. “I felt like I was a nonhuman being.”
Armed with Anderson’s Social Security number—obtained from a Medicare card that Lipski had intercepted—and a fake driver’s license, Lipski walked into stores and convinced cashiers to let her charge merchandise on Anderson’s accounts. To keep the accounts from getting maxed out, Lipski wrote checks stolen from other victims. She’d pay down the balances and use the cards until the bank discovered the checks were bad.
*Names of victim and perpetrators have been changed.
In February, Lipski’s attacks escalated. Her boyfriend got picked up with a loaded gun at a convenience store. The cops searched his car and found drugs. Lipski needed $10,000 for bail. She found it via a loophole in the security procedures at Anderson’s credit union, and she raided other victims. As collateral, Lipski pledged the equity in Anderson’s home.
Anderson had no idea, until she got an angry call from a bail bond company. She despaired of escaping the ordeal. “I wanted to go to sleep and not wake up, because I was so tired of it never ending, and I didn’t know what to do,” she says.
By April, Lipski’s life was unraveling too. She’d broken up with her boyfriend and fallen out with Dino and Brian, leaving her on her own. But she had one victim whom she could still burn: Helen Anderson. So Lipski went to Macy’s. It wasn’t until she returned home that she realized she’d forgotten her handbag.
“That’s meth right there,” Lipski says. “It gives you the self-confidence to walk into a public place, charge $2,000 posing as someone else, and leave a purse behind with everything the police need to convict you.”
Lipski went to Macy’s the next morning, but security had found the fake IDs. She fled before cops arrived. Six weeks later, detectives finally caught up to her. She was charged with ten counts of identity theft. She and her accomplices had stolen nearly $1 million by using the information of Helen Anderson and dozens of other victims.
When Anderson went to Lipski’s sentencing hearing in December 2013, she didn’t see the attractive woman she’d found in her home in October 2012. Lipski was now disheveled, with dirty hair. In her orange jumpsuit, she stared at the judge, never making eye contact with Anderson.
Prosecutors asked Anderson if she was aware of the plea deal they had struck: Lipski pleaded guilty to seven felony counts of identity theft and agreed to enter a residential drug-treatment program. If she stayed clean and didn’t re-offend, she would not have to serve more than the nine months of jail time she’d done.
In one way, Anderson was lucky. Only a tiny percentage of identity theft cases are successfully prosecuted. After she saw her tormentor, her anger softened. Lipski, she learned, had a young son. She was an addict whose mother had struggled with addiction. “If she can go to rehab, get off drugs, and make a life for herself in an honest way, then that’s what I hope for her,” says Anderson.
Today, Alice Lipski is working at a restaurant, and she is tested for drugs weekly. “I don’t know exactly what’s in store for me,” she says. “I need to give myself the opportunity to find out what I can do when I’m not doing something bad.”
Anderson’s stolen funds were restored, but, as she and many victims report, the real damage is psychological: the sense of violation, the knowledge that your personal details were compromised. After the attacks, Anderson sold her house and moved in with her mother. Striving to repair her credit, she’s been stymied by the paperwork. As for the possibility of being the victim of future fraud, Anderson is fatalistic. “My information is out there,” she says.
HOW TO AVOID BEING AN IDENTITY THEFT VICTIM
1. Lock your mailbox: Nearly 60 percent of Americans don’t use a mailbox that locks.
2. Limit the personal information you get in the mail by opening online accounts for your bank and credit cards: Forty-two percent of Americans over 50 don’t have online access to all their accounts.
3. Monitor your credit. Consumers can receive a free report every year from each of the three credit agencies. Request a report from a different agency every four months.
4. Take note of any inactive credit card accounts you have and close them.
5. If you’re thinking about purchasing coverage from an identity protection service, go to idtheftinfo.org, run by the Consumer Federation of America, to find out what protection you need and how much it should cost. And ask whether your insurance company, bank, or employer offers a free or low-cost service of its own.
Doug Shadel is the AARP state director in Washington and a founder of the Fraud Watch Network, a group of more than 700,000 citizens fighting fraud in their neighborhoods.