The newest threat to your safety on the road
What if we told you that hackers can remotely access your vehicle’s internal systems—in order to track your trip or even stop your engine mid-travel? It might sound like something out of a movie, but in 2019, the Washington Post reported on a hacker who claims he can do just that. And it wasn’t the first time the threat of hackers taking over vehicles had become a cause for concern. So, should you be worried? Read on to find out. And once you’re up to speed, learn about the other cybersecurity secrets hackers don’t want you to know.

Has it ever actually happened?
“In 2015, it was revealed that a Jeep Cherokee could be hacked remotely to mess with its settings,” says Ray Walsh, a digital privacy expert at ProPrivacy.com. “The hackers remotely turned the air conditioning on to max and began using the windscreen wipers while purposefully squirting wiper fluid onto the cockpit window.” The incident he’s referring to was actually performed by car hacking researchers, with a willing participant was behind the wheel. But, according to Walsh, it proved the threat of car hacking is not a purely theoretical one. Here are more everyday things you didn’t know could be hacked.

The potentially deadly consequences
In the case of the Jeep hack, Walsh says “it is theoretically possible that a victim could have their windscreen wipers locked while wiper fluid is forced to obstruct the driver’s field of vision. This could result in a high-speed collision, and potentially even a loss of life.”
But that’s not the only risk of such hacking. “The security researchers also found zero-day exploits that allowed them to paralyze the steering wheel while the car was in motion, disable the car’s brakes, and even cause unintended acceleration,” Walsh adds. “These are very serious dangers that open drivers up to a very serious potential threat to their life.” Whether you’re hacked or not, you need to know how to handle these 16 scary driving scenarios.

How carmakers responded
The auto industry was quick to jump into action after these vulnerabilities were exposed. Since then, Walsh says, “Chrysler has recalled 1.4 million vehicles to issue a fix. This serves as evidence that this was a real-world problem that could have caused a loss of life and not just a theoretical problem.”

But has it happened in real life?
Outside the research setting, no. “Thus far, no cases have been reported in the wild of car crashes resulting from this kind of cyberattack,” says Walsh. But that doesn’t mean car hacks haven’t taken place. “It is possible that cases exist of successful car hacks that have been assumed by the authorities to be regular car accidents,” he explains.
Of course, whether or not this has actually occurred is impossible to prove at this point. But Walsh maintains that it is possible. “The problem with car hacking incidents is that it is easier to presume that a road accident has occurred due to a loss of concentration or a driver’s mistake,” he explains. “This results in reports of car hacking being met with skepticism and could theoretically result in fatal car hacks going unnoticed.” This, however, is the most common cause of car crashes in the United States.

So, how concerned should consumers be?
Let’s put it this way: The threat is real. “As more smart cars hit the roads, the potential for these kinds of attacks is going to grow,” Walsh says. “Security researchers involved in hacking smart cars are extremely vocal about the fact that it is only a matter of time before hackers discover new methods of wirelessly hacking smart cars. When this happens, whether there is a risk to people’s lives will revolve around whether malevolent hackers or security researchers find the exploit first.” He adds that there is a very real danger that car hacking could be used for the purposes of covert assassination.

Pushing for the black box
Because of the very real risks, Walsh thinks that consumers should demand more of car manufacturers. “It seems important for car manufacturers to be charged with the burden of proof anytime that there are reports of unusual car activity,” he says. “This means smart cars [should] require the equivalent of a black box that records any possible outside interference in a way that cannot be concealed or tampered with (either by hackers or automobile manufacturers seeking to cover up problems with their cars). This kind of black-box technology will give consumers and the authorities some ability to properly ascertain wrongdoing should it be suspected.”

Smartphones may be partly to blame
Tom Lysemose Hansen is the Chief Technology Officer and founder of Promon, an app security company that has, in the past, exposed Tesla as not having a sufficient level of security to prevent smartphone hackers from locating a vehicle, unlocking its doors, and driving away in keyless mode. But this isn’t a problem that’s specific to just one company. “Out of convenience, we are increasingly turning our smartphones into remote controls for our cars, and, unfortunately, as we know, phones can be hacked, making the risk incredibly real,” he says. “When successfully hacked, connected car features then fall into the hands of cybercriminals.”

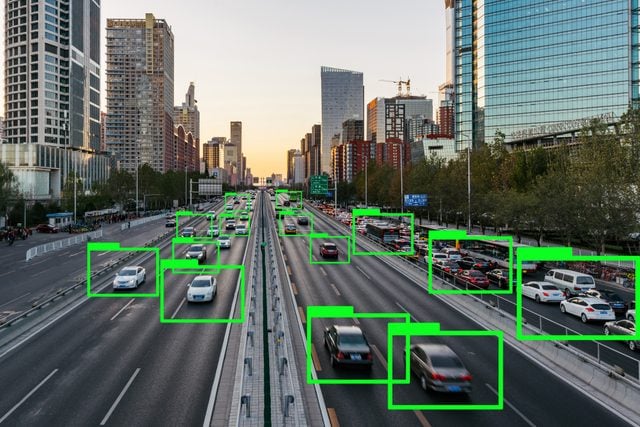
Smart cars pose the greatest risk
“Cars that are at risk of hacking tend to be smart vehicles that are connected to the Internet,” Walsh explains. “However, it is also possible for attackers to connect physically to a car’s systems either via the dashboard or via some other means to start tampering with its settings and features.” And this isn’t a risk that’s going away anytime soon. “By 2020, it is predicted that around 250 million cars will be connected to the Internet in order to provide onboard entertainment,” he says.
So, what are the potential risks, exactly? Our experts outline them below.

Hacker threat #1: Overriding the car’s keyless entry
Cars with keyless entry systems are the most likely to fall victim to this type of attack. “This is because radio transmitters are being sold online that give criminals the ability to spoof keyless systems to gain entry to cars and start them up,” Walsh explains. “So far, at least 110 cars from 27 manufacturers have been revealed to be at risk of this kind of hacking.” And if a criminal can hack your keyless entry system, they can easily enter your car and drive away. It’s the sneaky way thieves are targeting your car-key fob.

Hacker threat #2: Identity theft
“By tapping into your connected car, due to software vulnerabilities, cybercriminals can potentially steal and sell personal information,” Lysemose explains. Any information you have uploaded into your car’s system, or your car’s app on your phone, is potentially at risk.
“Beyond this,” Lysemose continues, “apps for connected cars can also be used by previous owners to bring up all kinds of information about [the car’s] current owner. Drivers of cars from BMW, Jaguar Land Rover, and Mercedes-Benz have reported that previous owners retain unrestricted access to the data and controls of connected cars after resale. It’s also widely documented that rental-car companies routinely fail to delete personally identifiable information that car-hire customers input into infotainment systems. A leak of this type of personal information, which potentially includes passwords, health data, and driving patterns, poses a significant security risk.” Make sure you know these signs you’re about to be hacked.

Hacker threat #3: Messing with your driving experience
As discussed earlier, hackers could potentially remotely control the various systems in your car. “This could mean turning on the radio or the air conditioning or even controlling the car’s self-driving features to steal the car or make it crash,” says Walsh. While a hacker messing with your radio may not seem like that big of a deal, the potential distraction as a driver attempts to figure out what’s going on could lead to an accident. Find out the car safety features no vehicle should be without.

Hacker threat #4: Hacking your USB port
According to a list of car hack vulnerabilities produced by esurance, your car’s USB port poses a significant risk because it can be attacked by viruses. Even just listening to music through the port could apparently infect your car with malware. And if your phone has been hacked, plugging it into the USB then gives the hackers access to your car’s systems. That’s just one of the reasons why you should stop charging your phone in your car.

Hacker threat #5: Intentional destruction
“Hackers have previously managed to engage car brakes remotely and even to accelerate against the driver’s will,” Walsh says. “And security researchers say it is only a matter of time before new wireless exploits are discovered in the wild.” If a hacker wanted to hurt someone and was able to access their car’s systems (or the systems of any vehicles driving nearby), this would be one way to accomplish that goal. Find out some car gadgets that immediately make driving safer.

To minimize the risks, keep your systems updated
Now that you know the risks, the question is: What can you do to protect your car and yourself? A lot, actually. The first thing you should do, says Walsh, is to stay “abreast of any information coming from [your] car manufacturer so that [you] can receive important patches and updates any time that they are made available.” You can accomplish this by ensuring your contact information is up to date with your car’s manufacturer and that you’ve enabled automatic updates whenever possible. It’s always a good idea to update your software—and not just in your car. Here’s what happens when you ignore the security warnings on your computer.

Be wary of outside software
“Consumers are also advised to be extremely careful when it comes to installing software onto their car’s onboard system,” Walsh says. “Installing software that is not manufacturer approved could create unexpected vulnerabilities that put car owners at risk. Consumers must be especially wary of third-party entertainment or remote diagnostic tools that have not been approved by their car manufacturer.” Find out some more things you should never do to your car.

Go old school
While the world moves in a newer, “smarter” direction, Walsh says there are some tools of the past that can still be extremely beneficial in protecting your car from theft. “Installing an old-fashioned anti-theft device on the steering wheel of a vehicle is a great deterrent that can stop consumers from being victimized by hacks revolving around keyless entry systems.”

Limit access
“Consumers should ensure that their car’s Wi-Fi and Bluetooth is always switched off whenever it is not in use,” Walsh says. If you aren’t sure how to do this, you should be able to consult your vehicle’s user manual or contact your car manufacturer directly. Plus, Walsh adds, it’s a good idea to keep your car’s Wi-Fi code hidden in a place that it can’t be easily discovered. In case you were wondering, here’s exactly how Bluetooth technology works.

Use antivirus software
“Finally, consumers must ensure that they properly use antivirus software to scan any USB dongles they intend to plug into their car,” Walsh explains. “Sometimes, official updates and patches may be made available to car owners via the Internet, and these can be flashed onto a USB dongle to patch the car and fix any newly discovered vulnerabilities.”
But he did add one final note of caution: “Consumers must be extremely careful anytime that they stick a dongle into their car, because it could potentially have been infected with malware that could give hackers a foothold into their onboard systems.”
